The Internet of Things (IoT) has been growing leaps and bounds since the last few years, strongly impacting business operations and our everyday lives. In this blog, we will see in detail how IoT has and is going to influence cybersecurity in the near future.
The continual evolution of the Internet of Things (IoT) has strengthened the feeling of connectivity in our lives by facilitating us with interconnected devices.
Know more: What Are The Predictions of People About IoT (Internet of Things)
A simple example of this is, today, we can control the cooling or lighting system at home, no matter which part of the world we are in. A commercial example is it makes processes smooth in the trucking industry.

But, amid all these amazing advantages and convenience, we can’t overlook the fact that IoT does bring in security vulnerabilities with its multiple, intercommunicating devices.
One loophole in one device and the entire network can suffer, compromising sensitive data and causing huge losses. That triggers the need for a stronger security mechanism. To achieve that, however, it is imperative to first understand IoT’s impact on cybersecurity.
IoT and Cybersecurity
With a string of internet-connected devices, the information transfer has become easier than ever. One can establish connection and communication between varying devices – right from a smartwatch and smartphone to an internet-connected refrigerator. As per Statista reports, the world would have around 75 billion IoT connected devices by 2025.
Read more: How to Develop IoT Apps Using the Minimum Viable Product Method
While that has made an individual’s life easier, it has facilitated seamless operations, increased productivity, and reduced overheads for businesses. The possibilities and opportunities regarding to IoT and its utility are many.
However, at the same time, it is also offering a backdoor to cyber-attackers as there are now more evolved ways and more internet-connected devices to hack into.
A survey by NETSCOUT states that it just takes about 5-minutes on an average to attack an internet-connected IoT device. Picture this – a hack into your IoT-connected air-conditioner could lead to the loss of your confidential data and financial information. This is just the beginning and the IoT infrastructure is constantly evolving.
According to the Business Insiders’ report, 38% of IoT developers expressed security as their top concern.
These figures speak volumes about the seriousness of the cybersecurity issues surrounding IoT. And interestingly enough, this is the same reason why cybersecurity is marching forward.
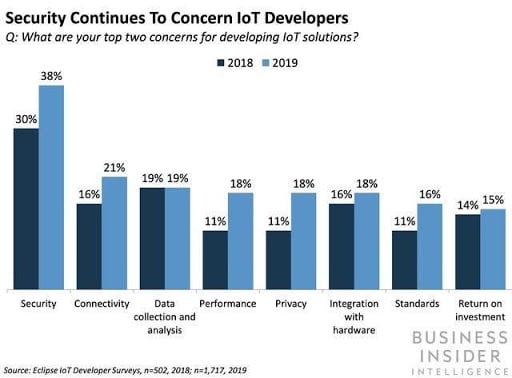
Source: BusinessInsider.com
Fueling the Need For New Security Technologies
In the world of IoT, there is very little space when it comes to regular updates to the processor or a common encryption file size. That is because a majority of these devices were developed with the limited battery life which only needed a humble processor that had a limited flash memory and consumed less power.
Learn more: What are the Challenges and Risks that are possessed by IoT & Blockchain
Apart from that, these devices are made to be intelligent – developed to aid humans and machines to provide them with the necessary information or help accomplish varied tasks.
Thus, if a hacker breaks into it, they can not only manipulate but also destroy the entire physical system, causing major life and economy threats.
Now those are indeed huge disadvantages from the security perspective. After all, at one end, we have advanced technologies, such as IoT, AI (artificial intelligence) and ML (machine learning), and on the other end, we’re relying on the same old security mechanisms.
With advancing technologies, there is a need for deeper security too, together with stronger device authentication and validation that becomes hard to break into.
IoT, with all its might, is encouraging the introduction and implementation of newer technologies of security so that the desired cybersecurity level can be attained across sectors.
Contemplating Blockchain Technology For Cybersecurity
The security models we have today are primarily centralized in nature. Moreover, such type of models ends up stretching the budget due to their high infrastructure as well as regular maintenance demands.
The scenario would worsen in the future when we would reach billions of IoT enabled devices globally. How?
Well, with such a large amount of devices, there would be massive connection and communication, which in turn, would congest the network and even cause it to fail entirely at some points.
The possible solutions to such restrictions can be found in the technology of blockchain. As we know, blockchain is a decentralized data structure, popular for its transparency, security, and resistance to data modification. IoT is pushing to explore more in this arena so that we can leverage the inherent blockchain characteristics to come up with a security model that’s layered and offers total privacy of the data.
Incorporating Proactive Approach a Must
In order to attain a watertight cybersecurity model, one can’t afford a reactive approach as a breach once done, results in damages that are often irreparable.
Therefore, a proactive approach is needed when outlining security solutions to the existing and potential threats. It is exactly what IoT is pushing for.
Companies should incorporate defense measures in their IoT devices. For that, first, they need to thoroughly understand the device, its working, the way it connects to a network, along with the loopholes and possible security problems.
Once these things are known, it becomes easier to pack the devices with the required security systems and firewalls. It tends to be more effective as well, compared to the method of releasing patches to fix vulnerabilities.
In addition to that, it is also demanding security compliance and regulations to keep pace with these rapidly evolving cyber-defense technologies.
Creating New Opportunities
While IoT is raising the level of complexity for information security, it is also creating demands for experts in the niche.
There is an increasing requirement for cybersecurity professionals in both personal (home entertainment devices, retail, personal medical devices) and critical (transportation, manufacturing, power generation, etc.) IoT infrastructure space.
Concluding Thoughts
IoT is continually transforming industries and our normal day-to-day lives, including the cybersecurity space as we saw above. With so many entry points and a huge amount of collected data, it is driving a change in the way cyber-defense is looked at and implemented.





Leave a comment